This week there’s major progress on privacy law reform, no progress on the online services’ esafety codes, a big tax change, and more. Oh, and some Chinese-made cameras were removed from government offices, while Woolworths installed more cameras in their supermarkets.
Continue reading “Digital developments from Canberra 25”Digital developments from Canberra 16
This morning Parliament wrapped up for 2022, and a whole bunch of important things happened — including the passing of legislation for the National Anti-Corruption Commission and bigger data breach penalties, and an interesting selection of new bills.
Continue reading “Digital developments from Canberra 16”The 9pm Tweaking of the Incompetent Brain Implants with Justin Warren
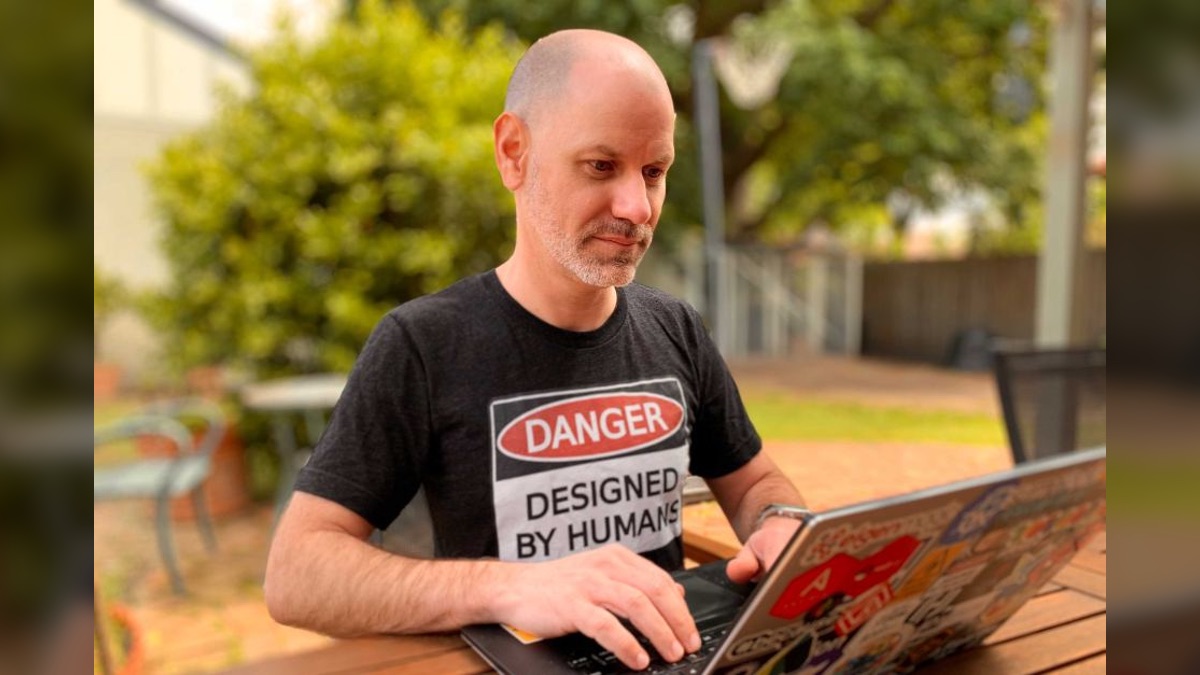
The Edict’s Summer Series 2022 concludes with special guest Justin Warren, “consultant, freedom of information tragic, hexagon enthusiast, and creator of the CyberRatingâ„¢ labelling scheme”.
Continue reading “The 9pm Tweaking of the Incompetent Brain Implants with Justin Warren”Weekly Wrap 611: Spooks, cynicism, conspiracies, and a slug
Monday 7 to Sunday 13 February 2022 was for me, and for so many Australians who pay attention to politics, a frustrating and stressful mess. But I won’t go into that here. I’ll just celebrate an interesting article, an even more interesting podcast, and a slug. A pretty slug.
Continue reading “Weekly Wrap 611: Spooks, cynicism, conspiracies, and a slug”Richardson Review: Chronology of Australia’s national intelligence community

In December 2020 the Australian government finally released the report of the the Comprehensive review of the legal framework of the National Intelligence Community, which was actually completed a year earlier. It includes this very handy chronology of the development of Australia’s national intelligence community.
Continue reading “Richardson Review: Chronology of Australia’s national intelligence community”Weekly Wrap 535: Getting ready for spring with a little reflection
August’s theme of low productivity continued through my week of Monday 24 to Sunday 30 August 2020, though I did managed to get something written. And I mapped out my podcast plans. And I enjoyed some sunshine now that spring seems to have arrived.
Continue reading “Weekly Wrap 535: Getting ready for spring with a little reflection”



